Discover our latest articles! Some articles are exclusively for our 'friends'. Want to become a friend? Join here.

Building Europe’s Digital Shield: How Collaborative DNS Security Is Powering National Resilience
Across Europe, governments and other critical infrastructure providers – like manufacturing, transpo
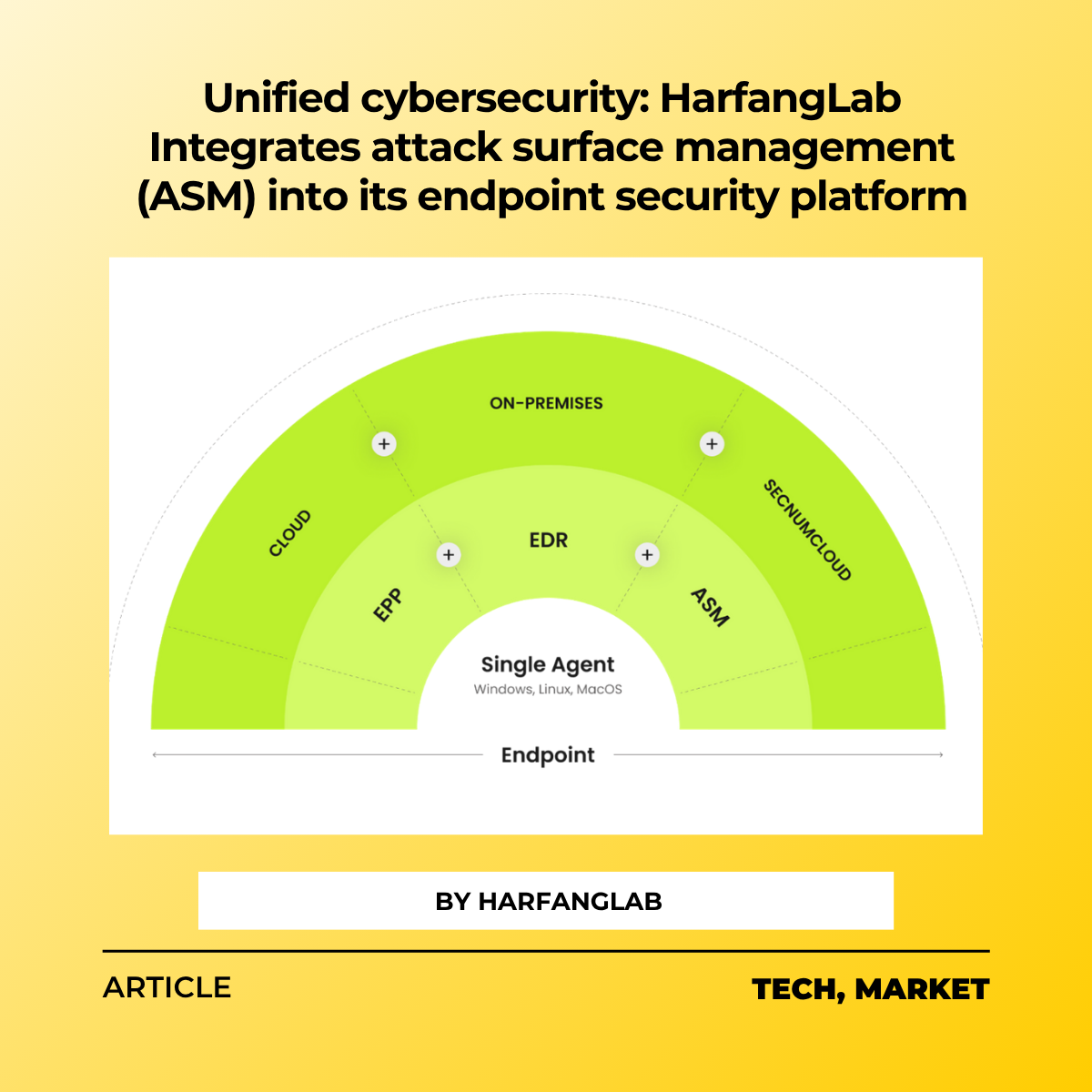
Unified cybersecurity: HarfangLab integrates Attack Surface Management (ASM) into its endpoint security platform
As the number of threats, vulnerabilities, and even security solutions continue to multiply, CISOs are facing an uphi

Cyberhive Ambassador Spotlight: Perspectives on European Cybersecurity: A Conversation with Ignacio Sbampato
Meet the Cyberhive Ambassador Ignacio Sbampato, Chair of the SME2Market Workstream and Chief Revenue

AI & Threat Hunting in the SOC: Augmentation Over Automation? Does Threat Hunting Still Belong to Humans?
It’s hard to avoid the noise around AI in cybersecurity.

ECSO Cyber Market Pulse- Summer Edition 2025
The Pulse is a compact and readable format designed for professionals seeking to learn about the European Cybersecuri

European businesses are rethinking digital dependencies and placing increased importance on sovereignty in cybersecurity
New research commissioned by European cybersecurity specialist HarfangLab shows performance alone is no longer enough
Blackout & Bright Side: How April 28 Tested Our Grids and Our Grit
Get to meet our content writer

Highlights Webinar with Atos Group and Labyrinth for Cyberhive Matrix H2 2025
On 10 June 2025, the European Cyber Security Organisation (ECSO) hosted an exclusive webinar to offi

Cyberhive Ambassador Spotlight: Paul Di Matteo from Trudexia on Tomorrow’s European Cybersecurity Landscape
Meet the Cyberhive Ambassador Paul Di Matteo!

ECSO Cyber Market Pulse May 2025
The Pulse is a new compact and readable format meant to be shared among professionals eager to learn about the Europe

Cyberhive Ambassador Spotlight: Régis Cazenave from S2 Grupo on Tomorrow’s European Cybersecurity Landscape
Meet the Cyberhive Ambassador Regis Cazenave!
